In today’s increasingly digital world, website security has become a top priority for businesses and individuals alike. One of the most common and dangerous threats that websites face is SQL injection. But what exactly is SQL injection, and why is it so important to understand and protect against it?
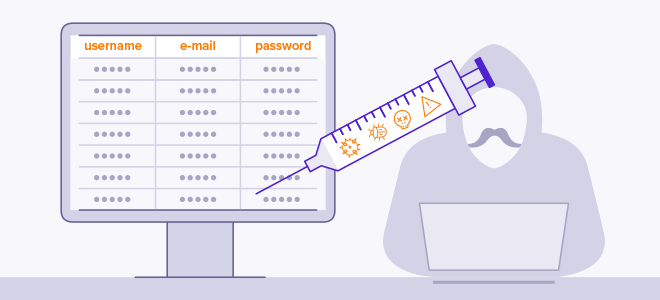
In this article, we will demystify SQL injection and shed light on the potential risks it poses to your website’s security. We will explore how hackers exploit vulnerabilities in your website’s code to gain unauthorized access to your database, potentially compromising sensitive information.
But fear not! We will also provide you with practical tips and strategies to protect your website from SQL injection attacks. By the end of this article, you’ll have a clear understanding of SQL injection, the steps you can take to safeguard your website, and the peace of mind that comes with knowing you’re doing everything you can to keep your online presence secure.
How does SQL injection work?
SQL injection is a hacking technique that takes advantage of vulnerabilities in your website’s code. To understand how it works, we need to first understand the role of SQL in web development. SQL, or Structured Query Language, is the language used to communicate with databases. It allows you to store, retrieve, and manipulate data.
In a typical web application, user input is collected through forms and sent to the server. The server then uses that input to construct SQL queries, which are used to interact with the database.
The problem arises when user input is not properly validated or sanitized before being used in these queries. This opens the door for attackers to inject malicious SQL code into the query, which can lead to unauthorized access to the database.
There are several ways in which SQL injection attacks can be carried out. One common method is through the use of a technique called “union-based” SQL injection. In this type of attack, the attacker manipulates the input in such a way that the original SQL query is modified to include additional statements that the attacker wants to execute. These statements can be used to extract sensitive information, modify data, or even gain administrative access to the website.
Another method is known as “blind” SQL injection. In this type of attack, the attacker is unable to directly see the results of their actions. Instead, they use a series of true or false questions to extract information from the database. This can be a slower and more time-consuming process for the attacker, but it can still be effective in certain scenarios.
It’s important to note that SQL injection attacks are not limited to websites that use SQL databases. They can also affect other systems that use SQL-like languages, such as NoSQL databases or even APIs that accept SQL-like queries.
In the next section, we will explore the risks and consequences of SQL injection attacks.
Risks and consequences of SQL injection
SQL injection attacks can have severe consequences for both businesses and individuals. The potential risks include:
1. Unauthorized access to sensitive information: By exploiting a SQL injection vulnerability, attackers can gain unauthorized access to your database. This means they can potentially access sensitive information such as user credentials, personal data, financial records, or any other data stored in your database. This can lead to identity theft, fraud, or other types of malicious activities.
2. Data manipulation or destruction: In addition to accessing sensitive information, attackers can also modify or delete data in your database. This can have serious consequences, especially if the data is critical for your business operations or if it affects the privacy and trust of your customers.
3. Website defacement or disruption: SQL injection attacks can also be used to deface your website or disrupt its normal functioning. Attackers can inject malicious code that alters the appearance of your website, displays inappropriate content, or even redirects visitors to other malicious websites. This can damage your brand reputation and result in the loss of customers.
4. Legal and regulatory implications: Depending on the nature of the data that is compromised, your business may be subject to legal and regulatory consequences. Data protection laws, such as the General Data Protection Regulation (GDPR), impose strict requirements on businesses to protect personal data. Failure to comply with these regulations can result in significant fines and legal liabilities.
Now that we understand the risks and consequences of SQL injection attacks, let’s take a look at some real-life examples to illustrate the impact they can have.
Real-life examples of SQL injection attacks
SQL injection attacks have been responsible for numerous high-profile data breaches and security incidents. These examples highlight the real-world impact of SQL injection vulnerabilities:
1. The Heartland Payment Systems breach: In 2008, Heartland Payment Systems, a major payment processing company, suffered a massive data breach that exposed over 130 million credit and debit card numbers. The breach was the result of a SQL injection attack that targeted a web application used for processing payments. The attackers were able to inject malicious code into the application, allowing them to capture cardholder data as it was being processed.
2. The Sony PlayStation Network breach: In 2011, Sony’s PlayStation Network was hacked, resulting in the theft of personal information, including names, addresses, and credit card details, of over 77 million users. The breach was attributed to a SQL injection vulnerability in a web application used for user authentication. The attackers exploited this vulnerability to gain unauthorized access to the database and steal the sensitive information.
3. The TalkTalk breach: In 2015, TalkTalk, a UK-based telecommunications company, suffered a major data breach that affected over 150,000 customers. The breach was the result of a SQL injection attack on a vulnerable web application. The attackers were able to extract customer data, including names, addresses, and financial information, by exploiting the SQL injection vulnerability.
These examples highlight the serious consequences of SQL injection vulnerabilities. It’s clear that no organization, regardless of its size or industry, is immune to these attacks. In the next section, we will discuss how you can identify if your website is vulnerable to SQL injection.
How to identify if your website is vulnerable to SQL injection
Identifying if your website is vulnerable to SQL injection is a critical step in protecting your online presence. Here are some methods you can use to check for SQL injection vulnerabilities:
1. Manual code review: Conduct a thorough review of your website’s code to identify any potential vulnerabilities. Look for instances where user input is used in SQL queries without proper validation or sanitization. Pay attention to areas such as login forms, search functionality, and any other input fields that interact with the database.
2. Automated vulnerability scanners: There are several tools available that can automatically scan your website for SQL injection vulnerabilities. These tools simulate attacks and check for common patterns and vulnerabilities in your code. While automated scanners can be useful, they should not be relied upon as the sole method of vulnerability detection.
3. Penetration testing: Hire a professional penetration tester to assess the security of your website. These experts use specialized tools and techniques to identify vulnerabilities, including SQL injection. They can provide valuable insights into the security posture of your website and recommend appropriate remediation measures.
It’s important to note that identifying SQL injection vulnerabilities is not a one-time task. As your website evolves and new features are added, it’s crucial to regularly re-evaluate your security posture and perform ongoing vulnerability assessments.
In the next section, we will discuss best practices to protect your website from SQL injection attacks.
Best practices to protect your website from SQL injection
Protecting your website from SQL injection attacks requires a multi-layered approach that combines secure coding practices, regular updates and patching, and the use of additional security measures. Here are some best practices to consider:
1. Use parameterized queries and prepared statements: Parameterized queries and prepared statements are techniques that allow you to separate SQL code from user input. This ensures that user input is treated as data rather than executable code. By using these techniques, you can effectively eliminate the risk of SQL injection vulnerabilities.
2. Regularly update and patch your software: Keep your website’s software, including the web server, database server, and any content management systems or frameworks, up to date with the latest security patches. Vulnerabilities in these systems are often discovered and patched by the developers, and neglecting to update them can leave your website exposed to known vulnerabilities.
3. Implement a web application firewall (WAF): A web application firewall can provide an additional layer of protection against SQL injection attacks. It acts as a filter between your website and the users, inspecting incoming requests and blocking malicious traffic. A WAF can detect and block SQL injection attempts, as well as other types of attacks.
4. Apply the principle of least privilege: Limit the privileges of database accounts used by your website to the minimum necessary for their intended functionality. This reduces the potential impact of a successful SQL injection attack by limiting the attacker’s access to sensitive data or functions.
5. Regularly monitor and log database activity: Implement a monitoring and logging system that tracks and records all database activity. This can help you detect and respond to SQL injection attacks in a timely manner. By monitoring the logs, you can identify suspicious patterns or anomalies that may indicate a security breach.
By following these best practices, you can significantly reduce the risk of SQL injection attacks on your website. However, it’s important to remember that no security measure is foolproof. In the next section, we will discuss additional security measures to strengthen your website’s defense against SQL injection.
Additional security measures to strengthen your website’s defense against SQL injection
While the previous section covered the fundamental security measures to protect against SQL injection, there are additional steps you can take to further strengthen your website’s defense. Consider implementing the following measures:
1. Input validation and sanitization: Validate and sanitize all user input to ensure it conforms to expected formats and does not contain any malicious code. This can help prevent various types of attacks, including SQL injection.
2. Database encryption: Encrypt sensitive data stored in your database to protect it from unauthorized access. Encryption ensures that even if an attacker manages to access the database, the data will be unreadable without the encryption key.
3. Multi-factor authentication: Implement multi-factor authentication for user accounts to add an extra layer of security. This can help prevent unauthorized access, even if an attacker manages to obtain valid login credentials through a SQL injection attack.
4. Regular security audits: Conduct regular security audits to identify potential vulnerabilities and weaknesses in your website’s security. These audits should include both technical assessments, such as vulnerability scanning and penetration testing, as well as policy and procedure reviews.
5. Employee education and awareness: Train your employees on best practices for website security and raise awareness about the risks of SQL injection and other common vulnerabilities. Human error is often a weak point in website security, so educating your team is essential.
By implementing these additional measures, you can further enhance the security of your website and minimize the risk of SQL injection attacks. However, it’s important to remember that security is an ongoing process. Regularly assess your website’s security posture and stay up to date with the latest security practices and technologies.
Conclusion
SQL injection is a serious threat that can compromise the security of your website and the sensitive data it stores. Understanding how SQL injection works and the potential risks it poses is the first step in protecting yourself against this type of attack.
By following best practices, such as using parameterized queries, regularly updating your software, and implementing additional security measures, you can significantly reduce the risk of SQL injection vulnerabilities. It’s also important to regularly assess your website’s security posture, perform vulnerability assessments, and stay informed about the latest security practices.
With a proactive approach to website security, you can ensure the safety of your online presence and the trust of your users.
So, take action today and protect your website from SQL injection!
Categories: Tech
Tags: sql sql injection tech
Leave a Reply